Kaspersky Total Security Télécharger 2025 pour Windows / Mac
Kaspersky Total Security Télécharger 2025 pour Windows et Mac
Guide complet de Kaspersky Total Security
Dans le monde numérique d’aujourd’hui, protéger vos appareils et vos données personnelles contre les menaces en ligne est plus crucial que jamais. Kaspersky Total Security est une suite de sécurité complète conçue pour vous protéger contre diverses cybermenaces et garantir la sécurité de votre vie numérique. Ce guide explique sa nature, son installation et sa configuration, ses fonctionnalités, ses options de support client, ses tarifs, ses avantages et inconvénients, l’expérience utilisateur, des comparaisons avec d’autres outils, des conseils pour une utilisation efficace et l’importance de maintenir la sécurité de votre système.
Qu’est-ce que Kaspersky Total Security ?
Il s’agit d’une solution de sécurité premium offrant une protection complète contre un large éventail de menaces en ligne, notamment les virus, les logiciels malveillants, les logiciels espions, les attaques de phishing, etc. Elle offre des fonctionnalités avancées pour sécuriser vos ordinateurs, vos appareils mobiles et vos données sensibles, ce qui la rend idéale pour les particuliers et les familles recherchant une protection robuste.
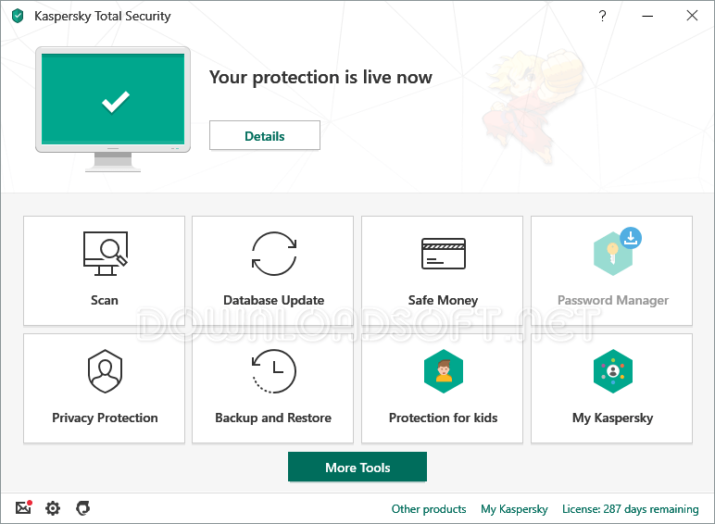
Caractéristiques principales
- Protection antivirus : Protection en temps réel contre les virus, les logiciels malveillants et autres menaces.
- Sécurité Internet : Protection contre les attaques de phishing, les sites Web malveillants et les escroqueries en ligne.
- Gestionnaire de mots de passe : Stocke et gère en toute sécurité les mots de passe de divers comptes en ligne.
- Safe Kids : Fonctionnalités de contrôle parental pour protéger les enfants en ligne.
- Sauvegarde et cryptage de fichiers : Outils pour sauvegarder et crypter les données sensibles pour plus de sécurité.
Installation et configuration
Guide d’installation étape par étape
L’installation de Kaspersky Total Security est un processus simple :
- Visitez le site Web officiel : Accédez au site Web de Kaspersky pour télécharger la dernière version du logiciel.
- Acheter une licence : Choisissez un plan d’abonnement et achetez une clé de licence.
- Téléchargez le programme d’installation : Après l’achat, téléchargez le fichier d’installation sur votre ordinateur.
- Exécutez le programme d’installation : Recherchez le fichier téléchargé et double-cliquez dessus pour démarrer le processus d’installation.
- Suivez l’assistant d’installation : L’assistant vous guidera à travers les étapes nécessaires, y compris l’acceptation du contrat de licence et l’activation du logiciel à l’aide de votre clé de licence.
Configuration initiale
Après l’installation, il est important de configurer efficacement Kaspersky Total Security :
- Exécuter une analyse complète du système : Lancez une analyse complète du système pour détecter et supprimer toutes les menaces existantes.
- Configurer les paramètres du pare-feu : Ajustez les paramètres du pare-feu pour contrôler l’accès au réseau et vous protéger contre les connexions non autorisées.
- Configurer le gestionnaire de mots de passe : Configurez le gestionnaire de mots de passe pour stocker et gérer vos mots de passe en toute sécurité.
Caractéristiques
Cette suite de sécurité offre un ensemble complet de fonctionnalités conçues pour améliorer votre sécurité en ligne :
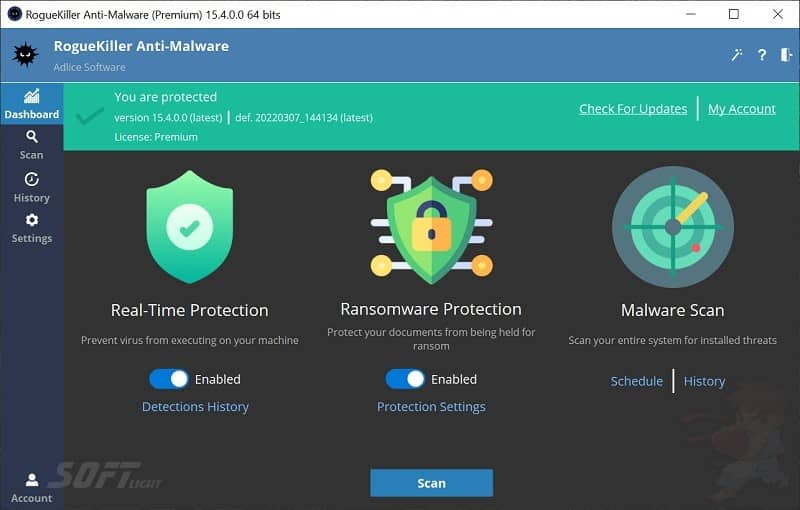
1. Protection antivirus avancée
Les capacités d’analyse et de détection en temps réel protègent contre les virus, les logiciels malveillants et autres logiciels nuisibles.
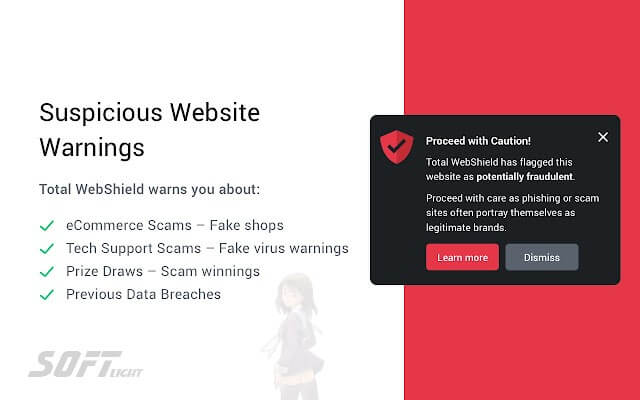
2. Navigation Internet sécurisée
Protections contre les attaques de phishing, les sites Web malveillants et les escroqueries en ligne, garantissant une expérience de navigation sécurisée.
3. Gestion des mots de passe
Stocke et gère en toute sécurité les mots de passe, ce qui facilite le maintien de mots de passe forts et uniques pour tous vos comptes en ligne.
4. Contrôle parental
Offre des fonctionnalités de contrôle parental robustes pour protéger les enfants des contenus inappropriés et gérer leur activité en ligne.
5. Sauvegarde et cryptage des données
Fournit des outils pour sauvegarder et crypter les données sensibles, ajoutant une couche de protection supplémentaire contre la perte de données et l’accès non autorisé.
Support client et centre d’aide
Ressources disponibles
Pour les utilisateurs ayant besoin d’assistance, cette solution de sécurité propose plusieurs options d’assistance :
- Documentation officielle : Des guides complets couvrant l’installation, l’utilisation et le dépannage sont disponibles en ligne.
- Centre d’aide : une section dédiée où les utilisateurs peuvent trouver des réponses aux questions et problèmes courants.
- Assistance par chat en direct : Accédez au support client via le chat en direct pour une assistance immédiate.
- Assistance téléphonique : Les utilisateurs peuvent contacter l’équipe d’assistance par téléphone pour une assistance personnalisée.
Contacter le support
Si des problèmes surviennent et ne peuvent pas être résolus par le biais des ressources d’auto-assistance, envisagez de contacter l’équipe d’assistance pour obtenir une assistance personnalisée.
Tarifs et forfaits
Kaspersky Total Security propose une variété de plans tarifaires pour répondre aux différents besoins des utilisateurs :
Plans d’abonnement
- Propose différents plans d’abonnement en fonction du nombre d’appareils et de la durée de la licence.
Options multi-appareils
- Fournit des options pour protéger plusieurs appareils, notamment des ordinateurs, des smartphones et des tablettes, sous une seule licence.
Avantages et inconvénients
Avantages
- Protection complète : Offre une large gamme de fonctionnalités de sécurité pour se protéger contre diverses menaces en ligne.
- Interface conviviale : Conçue pour une utilisation facile, la rendant accessible à tous les niveaux de compétence.
- Fonctionnalités de contrôle parental : Fournit des options de contrôle parental robustes pour protéger les enfants en ligne.
- Support client solide : Plusieurs options d’assistance garantissent que les utilisateurs peuvent obtenir de l’aide en cas de besoin.
Inconvénients
- Utilisation des ressources système : Peut consommer des ressources système importantes, affectant potentiellement les performances sur les ordinateurs plus anciens.
- Coûts d’abonnement : Les coûts d’abonnement continus peuvent être une préoccupation pour certains utilisateurs.
- Complexité : Certains utilisateurs peuvent trouver les fonctionnalités étendues écrasantes.
Expériences et témoignages d’utilisateurs
Commentaires positifs
De nombreux utilisateurs apprécient Kaspersky Total Security pour sa protection complète et sa simplicité d’utilisation. Les témoignages soulignent souvent l’efficacité du logiciel à détecter et bloquer les menaces.
Domaines à améliorer
Bien que les commentaires soient généralement positifs, certains utilisateurs suggèrent des améliorations dans l’utilisation des ressources système et les temps de réponse du support client.
Comparaison avec d’autres outils
Lorsque l’on compare cette suite de sécurité avec d’autres solutions de sécurité, plusieurs distinctions apparaissent :
Alternatives
- Norton 360 : Une suite de sécurité complète qui offre des fonctionnalités similaires mais peut avoir une interface utilisateur différente.
- McAfee Total Protection : Offre une protection robuste contre les menaces en ligne, mais certains utilisateurs la trouvent plus gourmande en ressources.
- Bitdefender Total Security : Connu pour ses puissantes capacités de détection des logiciels malveillants, il peut manquer certaines des fonctionnalités supplémentaires offertes par cette suite de sécurité.
Choisir le bon outil
Kaspersky Total Security dépend souvent des besoins individuels. Pour ceux qui recherchent une protection complète et un large éventail de fonctionnalités, cette suite de sécurité est une excellente option.
Conseils pour utiliser cette suite de sécurité
Meilleures pratiques
Pour maximiser l’efficacité de cette suite de sécurité, tenez compte des conseils suivants :
- Mettez régulièrement à jour le logiciel : Assurez-vous que le logiciel est régulièrement mis à jour pour inclure les dernières définitions de menaces.
- Exécutez des analyses régulières : Effectuez régulièrement des analyses complètes du système pour détecter et supprimer toutes les menaces potentielles.
- Configurer les paramètres du pare-feu : Personnalisez les paramètres du pare-feu pour contrôler l’accès au réseau et vous protéger contre les connexions non autorisées.
- Utilisez le gestionnaire de mots de passe : Profitez du gestionnaire de mots de passe pour créer et stocker des mots de passe forts et uniques.
Foire aux questions (FAQ)
A quoi sert cette suite de sécurité ?
Il est utilisé pour protéger les ordinateurs et les appareils mobiles contre les virus, les logiciels malveillants et autres menaces en ligne.
Est-ce que son utilisation est gratuite ?
Non, un abonnement est nécessaire pour une utilisation continue.
Puis-je l’utiliser sur plusieurs appareils ?
Oui, il offre des options pour protéger plusieurs appareils sous une seule licence.
Offre-t-il un contrôle parental ?
Oui, il comprend des fonctionnalités de contrôle parental robustes.
Comment puis-je obtenir de l’aide ?
L’assistance est accessible via la documentation officielle, les forums communautaires, le chat en direct ou l’assistance téléphonique.
Importance de la sécurité du système
Maintenir un système sécurisé est essentiel dans le paysage numérique actuel. Utiliser une suite de sécurité complète permet de protéger vos données et vos appareils contre les menaces potentielles.
Avantages d’une maintenance régulière du système
- Sécurité renforcée : Des analyses et des mises à jour régulières protègent contre les logiciels malveillants et autres menaces en ligne.
- Performances améliorées : Garder votre système propre et sécurisé peut améliorer les performances globales.
- Protection des données : Protection de vos données contre tout accès non autorisé et toute perte.
Tutoriels et ressources supplémentaires
Pour ceux qui cherchent à approfondir leur compréhension de cette suite de sécurité, diverses ressources sont disponibles :
- Documentation officielle : Guides complets couvrant l’installation et les fonctionnalités avancées.
- Tutoriels vidéo : Guides étape par étape démontrant comment utiliser efficacement différentes fonctionnalités.
- Communauté d’utilisateurs : Interagissez avec d’autres utilisateurs pour partager des trucs et astuces pour maximiser l’utilisation du logiciel.
Configuration requise
Avant d’utiliser Kaspersky Total Security, assurez-vous que votre système répond aux exigences suivantes :
- Système d’exploitation : Compatible avec les systèmes d’exploitation Windows et macOS.
- RAM : Un minimum de 2 Go de RAM est recommandé pour des performances optimales.
- Espace disque : Au moins 1,5 Go d’espace disque libre pour l’installation.
Conclusion
En conclusion, Kaspersky Total Security est un outil essentiel pour toute personne soucieuse de sa sécurité en ligne. Grâce à sa protection complète, son interface intuitive et ses fonctionnalités pratiques, il constitue une solution robuste pour préserver l’intégrité des appareils.
En comprenant ses capacités et en suivant les meilleures pratiques, les utilisateurs peuvent pleinement exploiter le logiciel pour renforcer leur sécurité numérique. Face à l’évolution constante des menaces, l’utilisation d’une suite de sécurité fiable reste essentielle pour protéger les informations sensibles.
Détails Techniques
- Catégorie : System Security
Nom du logiciel : Kaspersky Total Security
- Taille du fichier : 2,5 Mo
- Noyau : 32/64-bits
- Systèmes d’exploitation : Windows XP, Vista, 7, 8, 8.1, 10, 11 / Mac / Android / IOS
- Langues : multilingue
- Société développée : Kaspersky Lab
- Site officiel : kaspersky.com
Télécharger Kaspersky Total Security 2025